A 51 Attacker Can Potentially Do Which of the Following
The privacy-centric cryptocurrency network Grin GRIN has been the victim of a 51 attack according to a number of reports. An opening which an attacker has already used to perpetrate an attack.
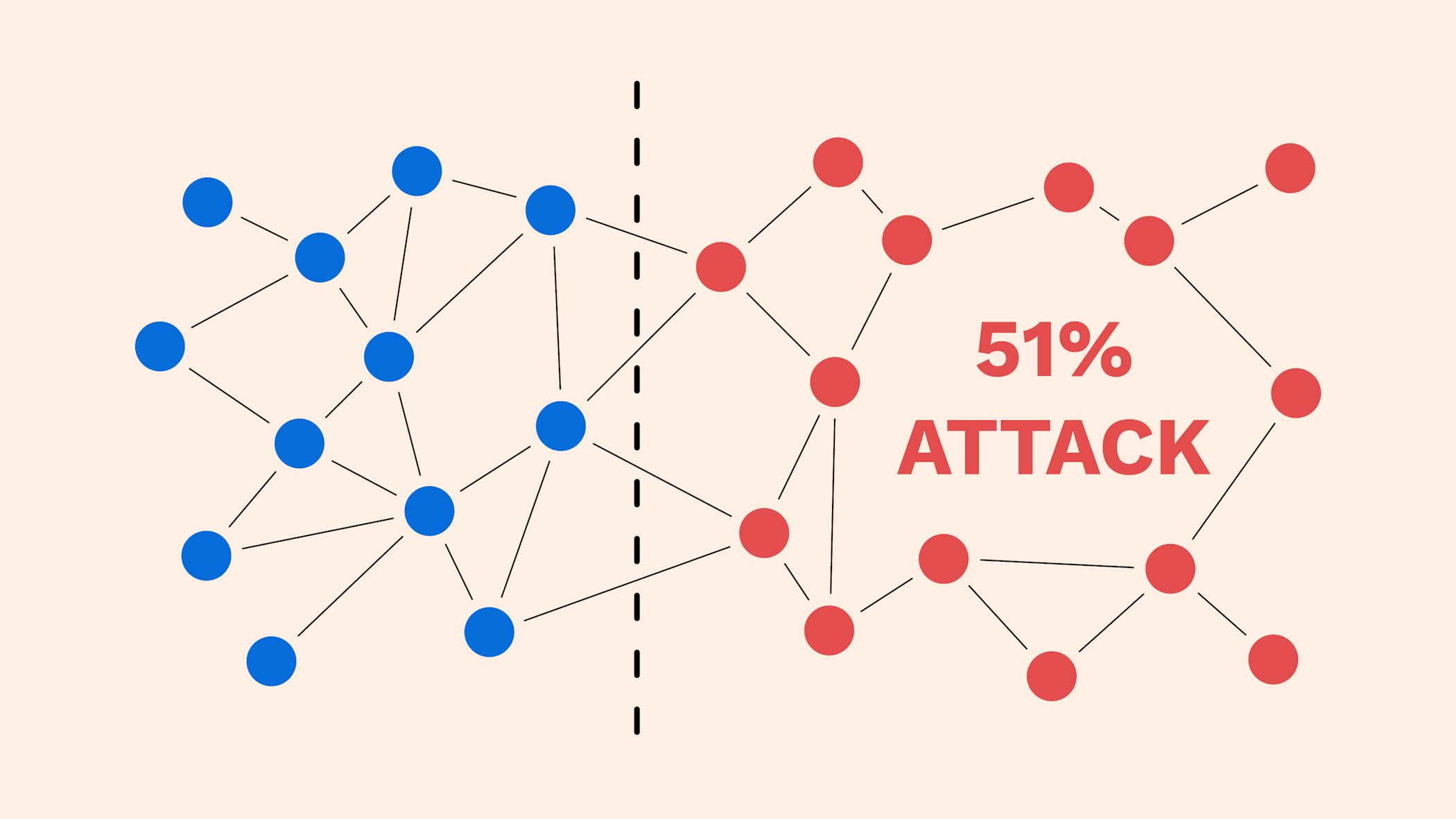
What Is A 51 Attack And How Is It Prevented Bitpanda Academy
Actual exam question from CompTIAs SY0-501.

. Which of the following methods of attack is an attacker most likely to use. Backdoors can also be installed by an attacker in hopes of gaining shell access to a server. Moreover the cost of such an attack is necessarily massive.
A weakness that can potentially be exploited by an attacker d. To reiterate a 51 attack does not enable the attacker to fundamentally change Bitcoin. For instance one can spend 5 bitcoins to purchase a.
He can not View the full answer Transcribed image text. In theory you might be able to set things up such that the cost of a 51 attack is necessarily greater than whatever financial gain you could get from it. Steal funds from a certain address.
As for waiting on confirmations it will help but only so much. A typographical error although not malicious is a failure to ensure integrity and would be considered an example of. 1 A 51 mining attacker CANNOT potentially A.
If a 51 attack costs 5000 per hour youre only going to do it if you can extract more than 5000 of value or if your motivation is to see the world burn. However Bitcoins proof-of-work consensus mechanism operates in such a way that an attacker would have to re-do the work that went into solving the cryptographic hash of each specific previous block. Attackers use 51 attacks to reverse transactions that have already taken place in a blockchain in what has come to be known as double spend.
Also while a 51 attacker can potentially erase old transactions it cannot fabricate new transactions using other blockchain network participants addresses as it is not possible to do so. A 51 percent attack can also theoretically allow someone to go back further in the blockchain and manipulate previous blocks and transactions. 51 or higher bestows some chance of forging a block on the attacker.
All SY0-501 Questions Which of the following BEST describes a network-based attack that can allow an attacker to take full control of a vulnerable host. Also while a 51 attacker can potentially erase old transactions it cannot fabricate new transactions using other blockchain network participants addresses as it is not possible to do so. Consists of the set of methods and avenues an attacker can use to enter a system and potentially cause damage.
The attacker sends coins to person A while sending the same coins to person B. Make it unprofitable for other miners to mine they all foow the longest-chain rule Negatively affect the coins value D. If the attacker had 100 for a week they could undo a weeks worth of blocks in that time.
Computer Science questions and answers. It merely enables the attacker to block new transactions and potentially double-spend transactions that were initiated after she obtained majority control. A miner employing a 51 attack can NOT.
QUESTION 24 An attacker has gained access when which of the following is true. Its notable that BitFury has become vocal and proactive about the issue of possible 51 attacks given its ability to potential to take the lead on any potential solution. The threat of a 51 percent attack became very real for many Bitcoin owners this week when the worlds largest Bitcoin mining pool GHashIO flirted with and may have even surpassed 51 percent.
Heres how a 51 attack can be used for double spending. 51 would probably only let a thief undo a small handful of blocks if that much - again if anyone has the math to back this up please post it. O Attackers code has been developed using TeraBIT O Attacker has sent phishing emails to victims employees O Attackers code is operating on the victims infrastructure O Attacker has created an account on the.
Steal coins from an existing address B. Create false transactions that never occurred. Censor transactions from the blockchain 2.
The process of restricting access to a resource to only permitted users applications or computer systems. Once an attacker gains shell access they can potentially escalate their privileges by exploiting kernel-level vulnerabilities to gain root access to the server which would allow them to take over other sites hosted on the same server. Allegedly an unknown entity.

Android For Hackers How To Scan Websites For Vulnerabilities Using An Android Phone Without Root Android Phone Android Hacking Websites
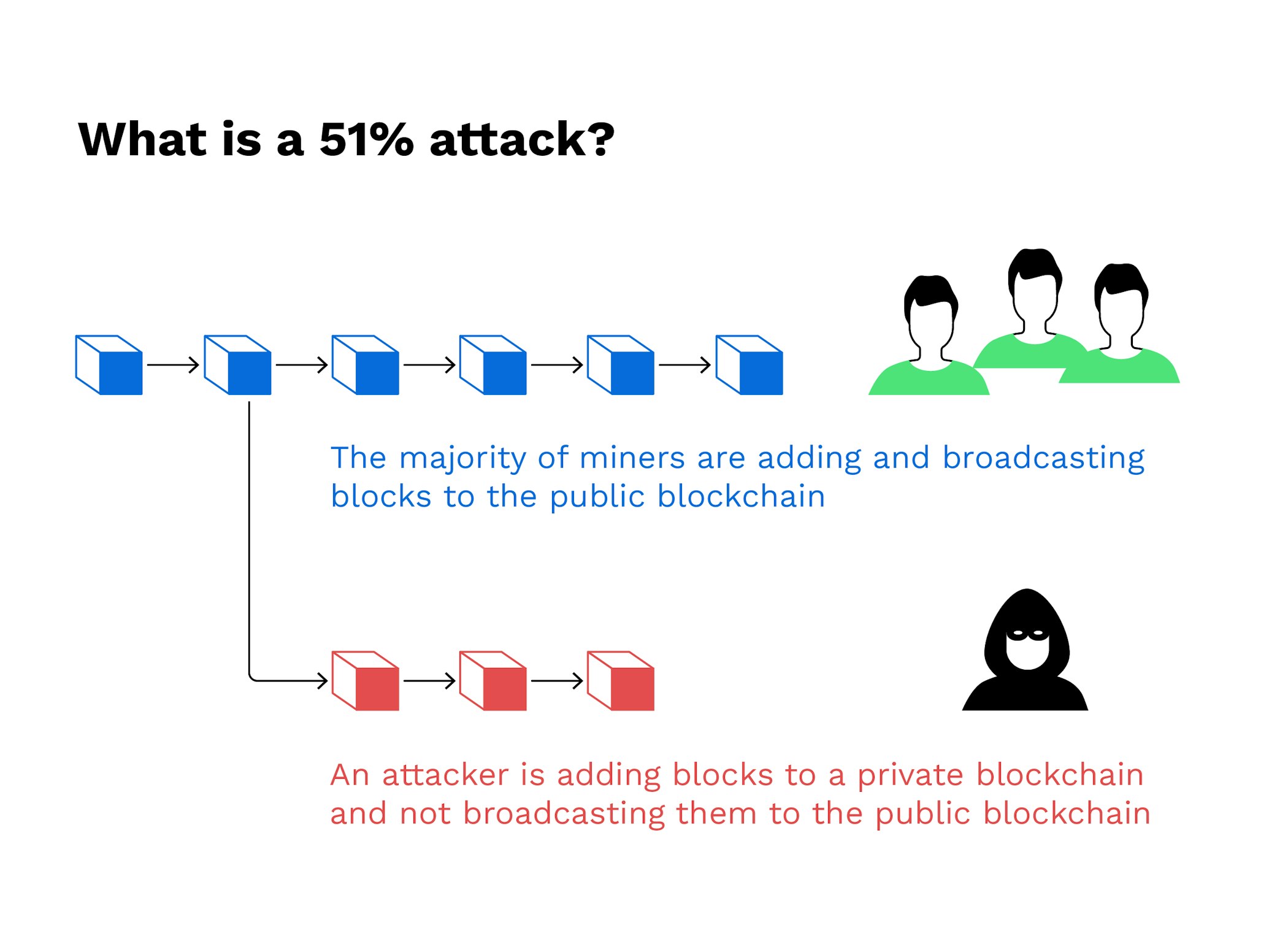
What Is A 51 Attack And How Is It Prevented Bitpanda Academy
Comments
Post a Comment